The 5-hour cyber security test

An Unfolding Energy Crisis
8th September 2022
Industrial action
8th January 2023Good morning and welcome to our Horizon Scanning newsletter.
As we enter Cyber Security Awareness Month, today’s bulletin examines data on how long it takes the average ethical hacker to access and export files. And our Toolbox looks, in more detail, and some of the different ways to stay safe.
Thanks for reading and stay safe.
The 5-hour cyber security test
As we enter Cyber Security Month, this piece from Forbes caught our eye. It has been compiled by Chuck Brooks, an expert in this field, and features some of the key stats on the present state of play.
The article reveals extraordinarily high numbers of phishing attacks in recent years – 1,097,811 in the second quarter of 2022 – with a dramatic increase on previous periods. (Indeed, phishing attacks are apparently at an all time high).
Brooks’ piece also finds that ethical hackers – individuals who are paid to test how easy systems are to break into – take around five hours to break in, collect and exfiltrate data. This is according to a new, first-of-its-kind survey of those in ethical hacker roles, carried out by Bishop Fox. The chart below breaks this down in more detail.
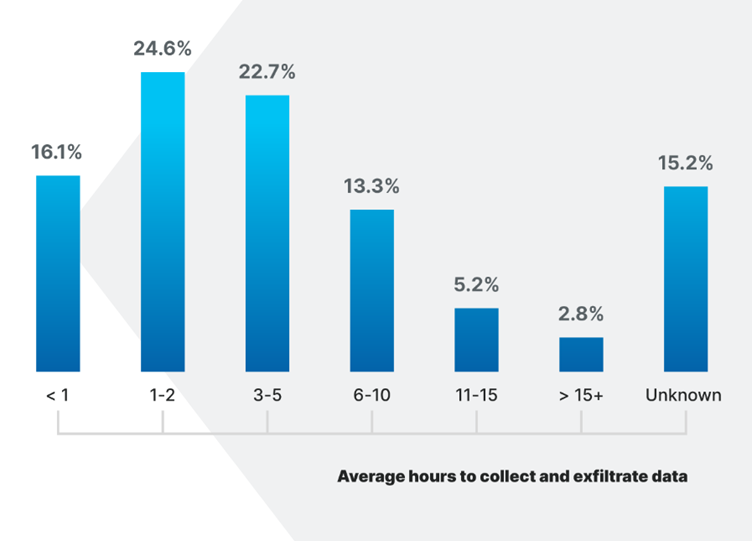
It is worth pausing to consider what a short period of time five hours is – the period between closing the door of the office at 5pm and switching on the 10 o’clock news.
Thankfully, the steps which organisations are taking is improving their efficacy in the fight against cyber crime and online attacks. But the pace at which new threats are emerging means that companies need to continually be updating, as different types of risk materialise.
Number one question for your business:
When did you last have your cyber security processes systematically tested by a third party?
Toolbox
Below are some further pieces of guidance and analysis, to strengthen your cyber resilience.
- The National Cyber Security Centre (NCSC) have released a package of support to help retailers protect themselves. If you run a retail business – or if you rely on retail firms as part of your immediate supply chain – then it’s well worth taking a look.
- This 10-step guide, also from NCSC, gives a clear route map for how an organisation can get themselves to the right place in terms of their resilience to online attacks. And this NCSC case study gives a handy example of good practice – based on the idea of a ‘layered’ approach to cyber security.
- Are municipal and public sector organisations vulnerable to ransomware attacks? This piece, which includes a 5-point checklist on how to protect yourself, says that they are. It reports that around 40% of UK incidents between September 2020 and August 2021 were aimed at the public sector. This is important to be aware of, both for national organisations and for firms who work with the government.
- Cyber security is not just the responsibility of technical staff or the board 🙅♀️
All staff need to be involved and understand their role in protecting themselves and others from cyber incidents National Cyber Security Centre have created a package of training for all staff in an organisation, that can either be used directly from our website or integrated into your organisation’s training platform https://www.ncsc.gov.uk/blog-post/ncsc-cyber-security-training-for-staff-now-available
- Lastly, this short report by Katalyst is an important one to look over. It includes an extremely valuable myth-busting section, for organisations looking to avoid complacency and stay on the front foot.
Thought for the week:
“The thing to really bear in mind with cyber crime is that, unfortunately, there is no end point. Businesses can never sit back, rest on their laurels and stop thinking about these issues. The battle for cyber security is between attacks which are continually becoming more sophisticated, and defences that are continually getting more robust. The most resilient organisations are those that always stay ahead of the curve.”
Gill Hall Resilience Consultant